Token-Based Authentication
Token-Based Authentication
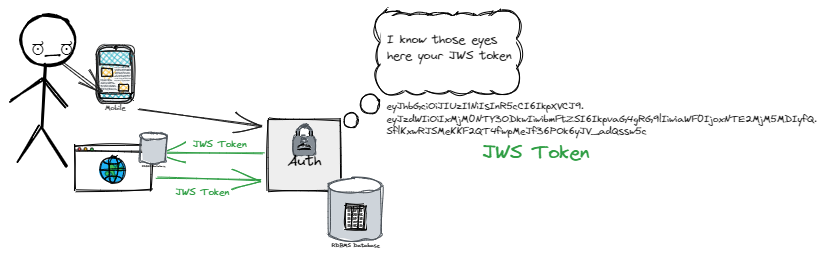
is a method of authentication that relies on the use of tokens to grant access to resources.
- Token information: username, roles, permissions, expiration date, metadata
- Can be signed with a secret key or using a public-private key pair (authenticity).
- The user starts to authenticate and receives a token from the server for future access.
- The user (device) only needs to authenticate once, and then he presents the token.
- Supports OAuth2, JWS, OpenID, and others
- Pros: stateless, the server doesn’t store user information in the session (scalability).
- Pros: secure, the token is encrypted and signed.
- Pros: If the token is stolen it has a limited lifespan.
- Pros: It is not dependent on specific devices, platforms, or domains.
- Cons: deciding about token storage, expiration time, and size.