Digital Signature
Digital Signature
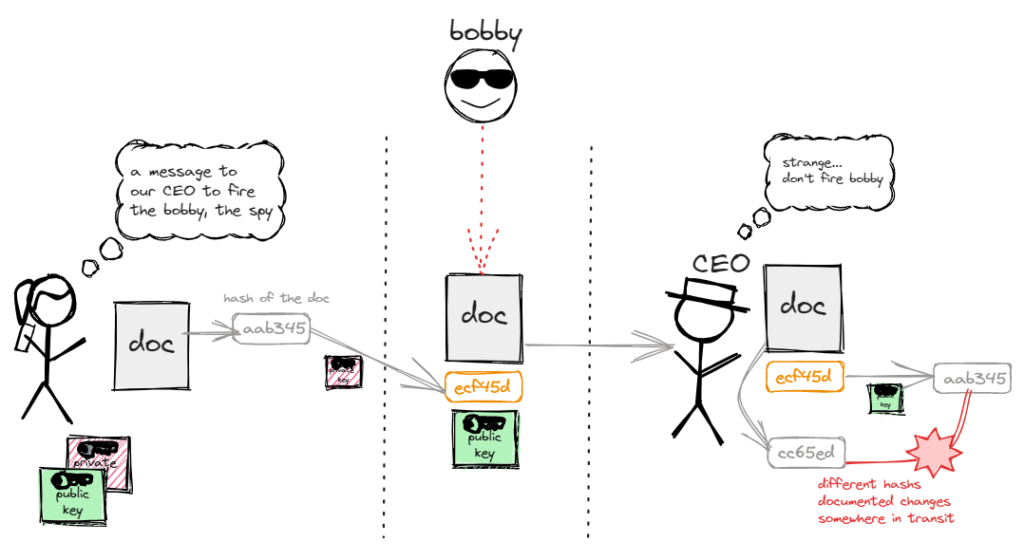
is a cryptographic technique that verifies the authenticity and integrity of a message, document, or transaction.
- It is like a fingerprint.”
- Two keys are generated: a public and a private.
- A hash is generated from the document or message.
- The hash is encrypted with the private key.
- The hash is appended to the document (along with the public key).
- The recipient uses the public key to decrypt the hash.
- A hash for the recipient is generated from the document or message.
- Both hashes should be equal.
- The idea is not to hide or encrypt the message but to make sure it is the original one.
- A digital signature provides integrity, non-repudiation, and authenticity to the message.
- In a war, when you receive a message, how do you know it was not tampered with by the enemy?